[ad_1]

Based on the U.S. Cybersecurity and Infrastructure Safety Company (CISA), whereas quantum computer systems are incapable of breaking public key encryption algorithms, private and non-private entities want to organize for future threats towards cryptography that’s not quantum resistant. Most of right now’s digital communications, together with cryptocurrencies, leverage public key encryption and CISA believes when “quantum computer systems attain greater ranges of computing energy and velocity, they are going to be able to breaking the general public key cryptography algorithms which might be in use right now.”
US Authorities Warns Nation-States and Personal Firms Are Actively Pursuing Quantum Computing Strategies That Might Threaten Present Cryptographic Requirements
Cryptocurrencies that leverage modern encryption strategies could possibly be damaged by quantum computer systems sometime, alongside different digital communications like electronic mail, messaging companies, and on-line banking. That’s in line with a current CISA report revealed on the finish of August. The U.S. authorities entity stresses within the report {that a} transition to post-quantum cryptography is important. “Don’t wait till the quantum computer systems are in use by our adversaries to behave,” CISA’s report particulars. “Early preparations will guarantee a easy migration to the post-quantum cryptography normal as soon as it’s out there.”
Discussions about whether or not or not quantum computing will have the ability to break public key encryption have been happening since scientists made progress entangling the primary pair of quantum bits (qubits) again in 1998. Quantum computer systems make the most of intricate physics with a view to calculate highly effective equations associated to right now’s modern crypto and mathematical techniques. Since 1998, tremendous quantum computer systems have improved with 14 calcium ion qubits entangled in 2011, 16 superconducting qubits in 2018, and 18 entangled qubits in 2018. CISA says quantum computer systems will create new alternatives however the tech additionally results in unfavourable penalties when it comes to encryption safety.
“Nation-states and personal corporations are actively pursuing the capabilities of quantum computer systems,” CISA’s report particulars. “Quantum computing opens up thrilling new prospects; nevertheless, the results of this new expertise embody threats to the present cryptographic requirements.”
Whereas Researchers Say Bitcoin’s Public Key Expertise Leverages ‘A number of Quantum-Resistant One-Means Hash Features,’ Some Blockchain Tasks Put together for a Submit-Quantum World
Cryptocurrencies like Bitcoin leverage modern encryption strategies and it has been mentioned many occasions over time that there’s a necessity to guard cryptocurrencies with post-quantum encryption. In 2020, when the commercial agency Honeywell revealed it constructed a quantum pc that successfully leverages six efficient qubits, crypto supporters began discussing quantum computer systems’ potential future results on Bitcoin and 256-bit encryption. Some digital forex supporters have already began making preparations for a quantum pc encryption-breaking occasion. Cambridge Quantum Computing is within the midst of working with Honeywell on a undertaking that “could be utilized to any blockchain community.”
Regardless of the efforts by cryptographers, some researchers wholeheartedly imagine large-scale quantum computer systems won’t ever come to fruition. Others suppose the timeline is far nearer than folks count on and some scientists have mentioned it could possibly be roughly 5 years from now. The Nationwide Institute of Requirements and Expertise (NIST) thinks 15 years is extra cheap. In the meantime, Ethereum builders have been researching quantum resistance alongside the Hyperledger Basis’s distributed ledger undertaking Ursa. Cryptographers making ready for a post-quantum world imagine encryption strategies like AES-128 and RSA-2048 won’t present sufficient safety towards quantum pc assaults.
Andreas Antonopoulos: ‘Satoshi Nakamoto’s Little Genius Design Ingredient Is Not an Accident’
The controversy has raged on for years and many individuals suppose the federal government’s warnings and the current quantum-based technological achievements by Honeywell, Google, Microsoft, and others, are the incentives folks have to embrace post-quantum cryptography.
Many articles, analysis studies, and mainstream headlines declare quantum computing will break any modern encryption and even forecast visitors jams and accidents nicely earlier than they occur. Nonetheless, Bitcoin proponents have mentioned on numerous events that the SHA256 encryption employed by Satoshi’s creation is a formidable foe towards a post-quantum world.
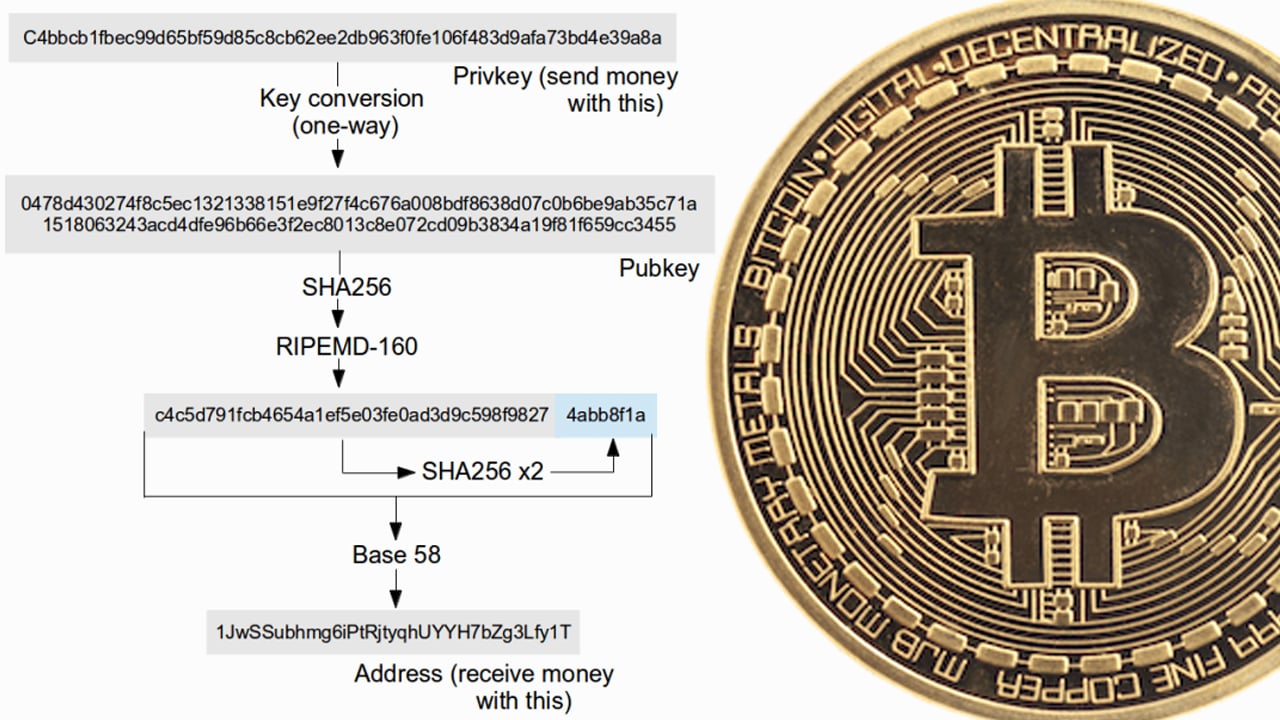
“In Bitcoin your public key isn’t (initially) made public. When you share your bitcoin tackle with others in order that they’ll ship you bitcoins, your bitcoin tackle is just a hash of your public key, not the general public key itself,” software program developer and cryptocurrency proponent Chris Pacia wrote in 2014. “What does that imply in English? A hash operate is a one-way cryptographic operate that takes an enter and turns it right into a cryptographic output. By one-way, I imply that you would be able to’t derive the enter from the output. It’s type of like encrypting one thing [and] then shedding the important thing.”
The software program developer’s 2014 paper on the topic concludes:
All of that may be a difficult method of claiming that whereas an attacker with a quantum pc may derive the personal key from the general public key, he couldn’t derive the general public key from the bitcoin tackle for the reason that public key was run by way of a number of quantum-resistant one-way hash features.
In a video that includes the bitcoin evangelist Andreas Antonopoulos, he mentioned that utilizing completely different bitcoin addresses each time is essential to bitcoin safety. Antonopoulos careworn that Satoshi’s two cryptography design selections are “completely genius.” “What you employ, which is a Bitcoin tackle, is a double-hashed model of your public key — which signifies that the general public secret’s by no means seen by anybody till you declare it by spending the transaction … This little genius design component will not be an accident,” Antonopoulos additional mentioned in his keynote speech. “What it does is, it creates a second layer abstraction of the underlying cryptographic algorithm utilized in elliptic curve digital signatures permitting you to do future upgrades.”
Antonopoulos continued:
Which signifies that the previous is safe as a result of it’s hidden behind the second veil of a distinct algorithm and the longer term could be modified as a result of you may current an tackle that’s not the hash of an elliptic curve, or its the hash of a distinct elliptic curve, or its the hash of an even bigger elliptic curve, or its the hash of a signing algorithm that’s quantum-resistant that has nothing to do with elliptic curve. So, you are able to do forwards modification to safe the longer term, and also you’ve received backwards safety as a result of you may have hid the previous.
What do you concentrate on the U.S. authorities’s current warning about quantum computer systems? Tell us what you concentrate on this topic within the feedback part under.
Picture Credit: Shutterstock, Pixabay, Wiki Commons, Chris Pacia, Bitcoin Not Bombs,
Disclaimer: This text is for informational functions solely. It’s not a direct provide or solicitation of a proposal to purchase or promote, or a advice or endorsement of any merchandise, companies, or corporations. Bitcoin.com doesn’t present funding, tax, authorized, or accounting recommendation. Neither the corporate nor the writer is accountable, straight or not directly, for any injury or loss induced or alleged to be attributable to or in reference to the usage of or reliance on any content material, items or companies talked about on this article.
[ad_2]
Source link





